Advance, automated endpoint protection, detection, and response
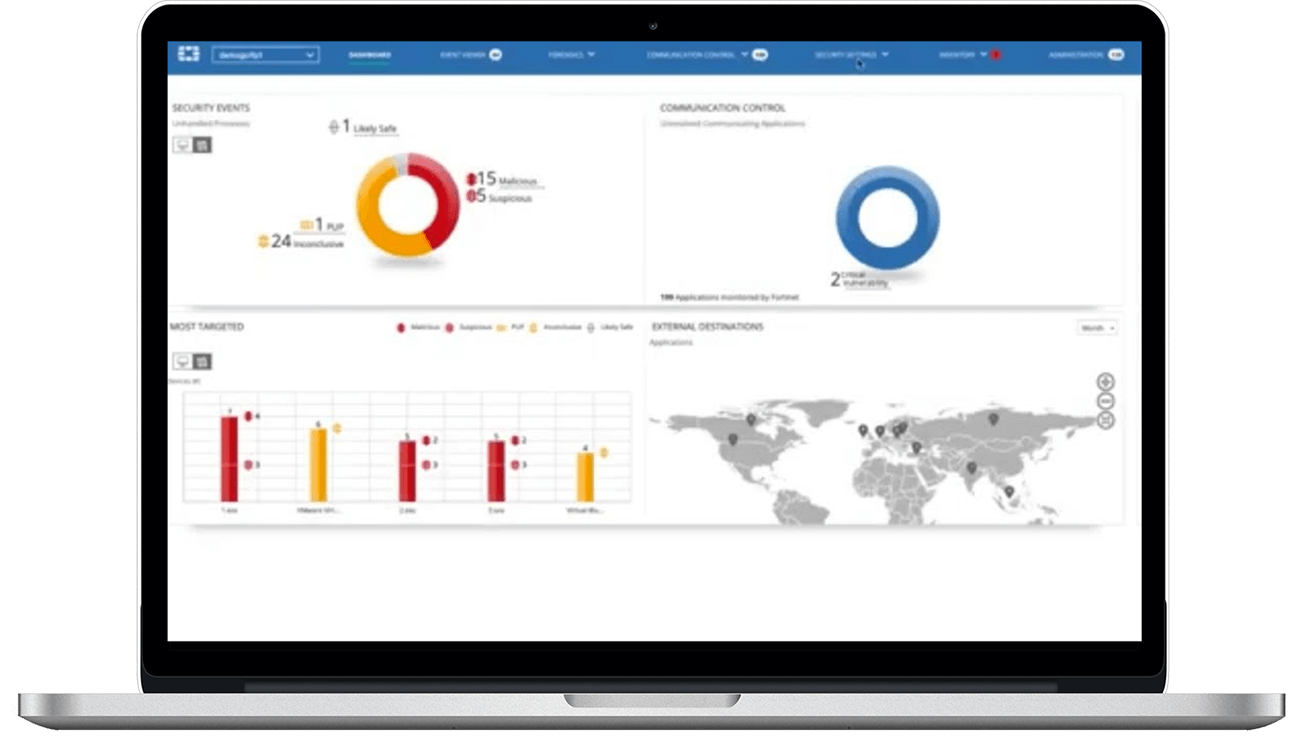
FortiEDR delivers advanced, real-time threat protection for endpoints both pre- and post-infection.
FortiEDR delivers real-time, automated endpoint protection with the orchestrated incident response across any communication device — including workstations and servers with current and legacy operating systems as well as manufacturing and OT systems — all in a single integrated platform, with flexible deployment options and a predictable operating cost.
Real-Time Proactive Risk Mitigation & IoT Security
Enable proactive reduction of the attack surface, including vulnerability assessment and proactive risk mitigation-based policies.
Pre-Infection Protection
Provide the first layer of defense via a custom-built, kernel-level Next Generation machine-learning-based Anti-Virus (NGAV) engine that prevents infection from file-based malware.
Post-Infection Protection
Detect and stop advanced attacks in real-time, even when the endpoint has been compromised. No breaches, no data loss, no problem.
Features
Discover and Predict
Deliver the most advanced automated attack surface policy control with vulnerability assessments and IoT security.
Malware Prevention
Use a machine learning antivirus engine to stop malware pre-execution allowing users to assign anti-malware protection to any endpoint group without requiring additional installation.
Detect and Defuse
Surgically stop data breach and ransomware damage in real-time, automatically allowing business continuity even on already compromised devices.
Respond and Remediate
Streamline incident response and remediation processes, manually or automatically roll back malicious changes done by already contained threats — on a single device or on devices across the environment.






