I have the chance every week to talk with organizations that come back through our executive briefing center. They share info concerning their strategic business and security initiatives whereas learning concerning our company vision and ways that we are serving customers with similar challenges to those they face.
Many times their stated interest is SD-WAN and cloud, typically segmentation, and different times security operations. without a question, these are necessary (and hot) topics, however, I perpetually try to carve out a bit little bit of time to speak concerning email security, and here’s why.
Industry data Shows Email may be a prime Attack Vector
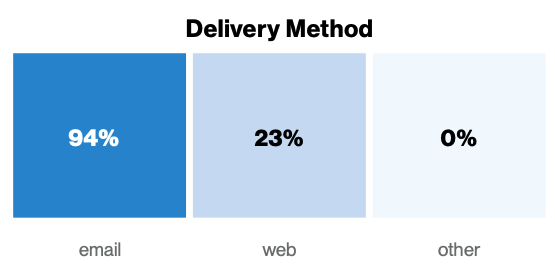
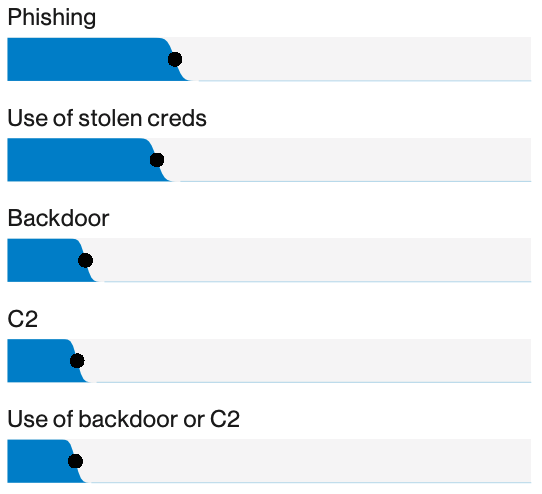
If you read the recent 2019 data Breach Investigation Report from Verizon, you’ll notice that ninety-four of malware was delivered via email which the highest cybercriminal action resulting in a breach was phishing.
FortiGuard Labs habitually finds new phishing campaigns rising to the fore, like this new version of Hawkeye that recently hit our weekly threat intelligence newsletter and blog.
But it’s not simply malicious files or URLs in an email that represent a risk. according to the Federal Bureau of Investigation, over 2 years of Business, Email Compromise exposed victims to a calculable loss of $3.3bn. And the U.S. Department of Justice recently filed suit against a cybercriminal purported to have taken $100m using that sort of fraud.
Email is Moving to the Cloud
Whether your organization uses Microsoft office 365, Google G-Suite, or another cloud-based email provider, email infrastructure is moving off-premises and into the cloud to be managed by some other person. This makes excellent sense given the maturity of email systems and increasing IT specializes in different high-value aspects of digital transformation.
However, outsourcing email infrastructure doesn’t essentially mean you must outsource email security. Given the industry data on top of this, this is often a really necessary question for every organization to answer concerning their distinctive appetite for risk.
Leading industry Analysts Assert you want to Re-Assess Email Security architecture
Recently, Gartner published their Market Guide for Email Security and declared that “Security and risk management (SRM) leaders should come back their organizations’ email security architecture within the light of current email threats, like refined malware, links to exploit kits, credentials phishing, and BEC.”
This Market Guide states “the following capabilities are often used as primary differentiators and choice criteria for email security products:
- To Protect Against Attachment-Based Advanced Threats: Network Sandbox and Content Disarm and Reconstruction
- To Protect Against URL-Based Advanced Threats: URL rewriting and Time-of-Click Analysis and web Isolation Services
- To Protect Against Impersonation and Social Engineering techniques utilized in URL-Based, Attachment-Based and Payloadless Advanced Threats: show Name Spoof Detection, Domain-Based Message Authentication, reporting and conformance on arriving Email, Lookalike Domain Detection, and Anomaly Detection.”
(Side note: we are proud to possess been listed among the Representative Vendors for international SEGs in Gartner’s 2019 Market Guide for Email Security.)
Conclusion
To recap, sources have known email-based malware, phishing, and BEC as pricey – and infrequently, the highest – cybercriminal actions. For those organizations rapidly moving to cloud-based email systems, this issue remains, and even as with their traditional email solutions, they’ll still ascertain whether or not the native email security is sufficient. additionally, leading analysts assert that each organization should re-assess their email security architecture.
Given this information, it looks pretty clear to me what we tend to all ought to embrace among our 2019 security projects.





