The Cybersecurity
Threat Landscape
in the Philippines 2022

As a remote working, hybrid workplace, and digitalization continue to rise in 2022, the risk of cyberattacks remains high. While these tech trends grow, the amount of data created increases as well. Cyber attackers take advantage of this transitory period through data breaches that target small and medium-sized organizations.
In this infographic, we will be walking you through what the current Philippine cybersecurity threat landscape looks like this year. Afterward, and more importantly, we will show you how you can combat this by deploying a zero-trust architecture.
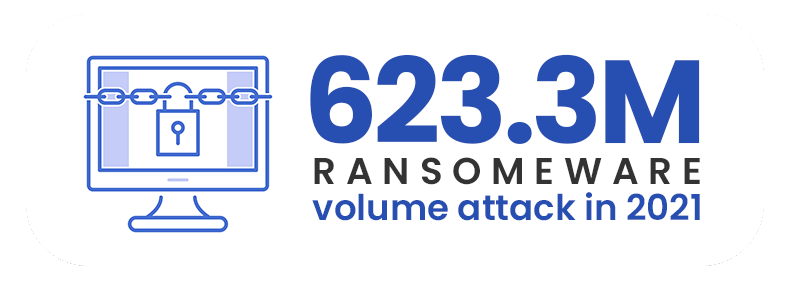
While ransomware is not necessarily a new form of cyberattack, the strategies of bad actors have evolved and continue to seep through the cracks of outdated cybersecurity systems in the Philippines. And in a recent study, the ransomware attack volume rose to 623.3 million in 2021. This alarming figure is 105% higher than 2020’s numbers.
Today’s ransomware tactics can be best described as double-extortion. To force organizations to pay the ransom, attackers exfiltrate and take crucial company information. If this isn’t enough trouble already, they threaten that they would leak or sell the data on the dark web if the victims would not pay within a given time.

Malware shares an equally intrusive and destructive nature as ransomware and has the same goal of infiltrating and stealing information. With this umbrella term, we will discover, according to the same study mentioned earlier, a staggering 5.4 billion malware attacks occurred last year. And compared to 2020, malware attacks skyrocketed to 167% in 2021.
Ransomware and malware typically start with a phishing email. Carrying this out will be child’s play and will cost little to nothing for the attackers. And yet, over the years, this strategy has still been so effective in gaining access to an entire corporate network. You can prevent this when you train and educate your workers on how to be aware of this threat. Boost your cybersecurity this 2022 to ensure the protection of your people and your company too.
The Attack Surface is Expanding
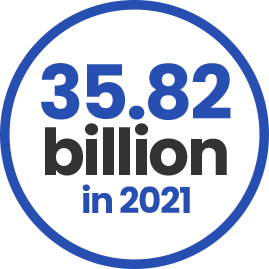
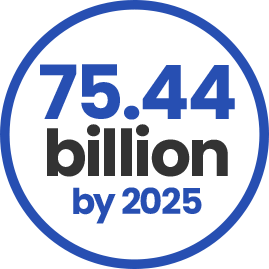
Multiple reports forecast that IoT (Internet of things) devices will grow from 35.82 billion in 2021 to 75.44 billion by 2025. This is a welcome development towards a more convenient and interconnected world from appliances to smartphones. But on the other hand, bad actors are now switching gears and are finding new entry points to exploit.
As our work environments evolve and grow, facing this would cause various challenges for IT teams as they try to keep up in protecting as many vulnerabilities as possible in the best way they can. Experts advise taking a holistic and integrated approach to cybersecurity this 2022. This unified approach would be beneficial since this would efficiently defend against the growing number of cyberattacks.
Rapid Adoption and Migration of Cloud



In 2020, six out of 10 businesses decided to move their work to the cloud. In another recent report published this year, 63% of SMB workloads and 62% of data will reside in a public cloud within the next 12 months. The numbers show the high level of trust these companies place in cloud computing.
Cloud services and solutions exploded in the last few years. Aside from migrating valuable data, many organizations had to speed up migrating entire systems to the cloud.
Cloud providers offer a basic level of security, but it would be best not to simply rely on this alone. The responsibility of securing a cloud infrastructure ultimately lies in the organization.
Going Beyond Passwords and Multi-Factor Authentication


Nowadays, having a simple password isn’t enough as your defense against cybercrime. Multi-factor authentication (MFA) takes a step further by adding a second, third, or more factors to the login process. Some of its advantages include ease in deployment and keeping accounts secure even if a password has been compromised. But not many companies see its value.
With all the gaps we’ve seen in the current cybersecurity scene in the Philippines, we need a more effective way to keep our data, resources, and people safe. This leads us to the need for a solution that has a fresh approach to the concept of trust.
What is Zero-trust Architecture?
Zero-trust security is founded on the principle: “never trust, always verify.” This means no one has automatic access to anything. All code, systems, and people are required to request access to data and other assets. This architecture helps proactively protect data with visibility and control that would lessen the burden on overwhelmed IT personnel who had to mitigate every risk and breach in the past.

By investing in and prioritizing this cybersecurity solution, enterprises would be able to operate more effectively regardless of the circumstances. Other benefits include:
- Reduced infrastructure complexity
- Secure access for those working in hybrid cloud and on-site environments
- Secure access for those working on a variety of devices
- Compliance with internal and regulatory standards
According to a recent survey, 83% of security and risk experts consider zero-trust a critical strategy for their companies, with 80% planning to fully adopt it this 2022.
Cybersecurity Solutions You Can Trust
For more than two decades in the industry, we have shown our competence in providing cybersecurity solutions tailored to the specific needs of any organization in any industry. We can deploy the zero-trust architecture you need to secure all the bases of your company network today and for years to come.
Ready to Get Started?
Ready to
Get Started?
Connecting with MEC provides you with access to globally recognized technology brands and a range of premium value-added services.

